He had a convincing fake passport, a surgically altered appearance, and years of practice living under another name, but AI-driven biometric scanners at a European airport saw through the disguise before the false identity reached the gate.
WASHINGTON, DC
The man at passport control looked calm because he had spent years preparing for that moment, carrying a passport that appeared genuine to the eye, wearing an older face shaped by time and cosmetic alteration, and moving with the confidence of someone who believed the border still depended on paper.
The officer did not see panic because there was none, at least not at first, since the traveler had crossed cities, rented rooms, moved money, changed phones, and built a life around the belief that documents remained the central weakness of international security.
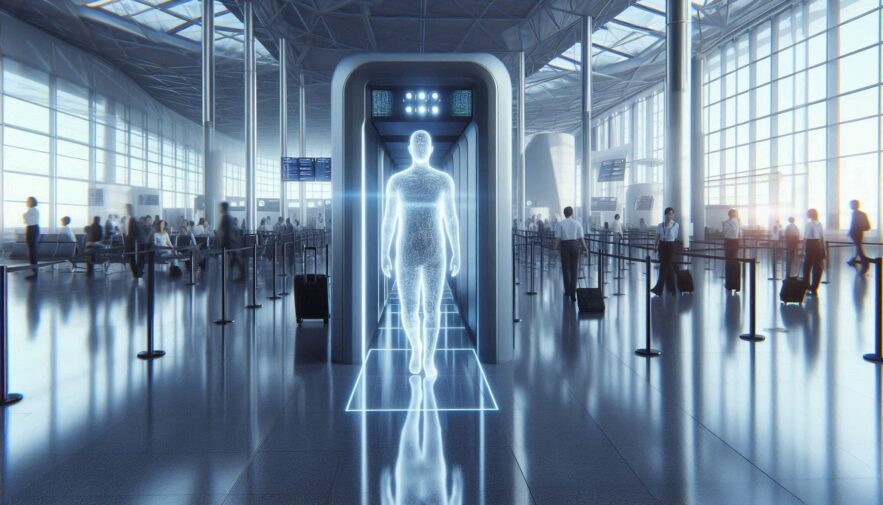
Then the biometric gate refused to accept the story, because the facial comparison system did not care about the name printed in the passport, the careful grooming, the altered features, or the practiced answers prepared for a human inspector.
The old passport trick failed because the border was no longer reading only the passport.
For decades, fugitives and document brokers believed that a strong passport, a believable travel history, and a disciplined personal story could move a person through airports with limited scrutiny.
That world is disappearing because modern border systems increasingly compare the person, the passport, the chip data, the travel record, the facial image, the fingerprints, the entry history, and the risk signals surrounding the journey.
The European Union’s full implementation of the Entry/Exit System has accelerated this transformation by replacing traditional passport stamping with digital records that include travel document data, entry and exit details, facial images, and fingerprints for non-EU short-stay travelers through the EU’s Entry/Exit System.
The shift matters because a forged or fraudulently obtained passport can no longer stand alone as the main proof of identity when the person presenting it must also survive biometric comparison against government and border databases.
The passport is now only one part of the inspection, and the face in front of the camera has become its own credential.
The face became the evidence that the document could not explain.
Facial recognition does not identify a person the way a friend does, because it measures and compares patterns across features, proportions, distances, textures, and relationships that may remain detectable even when a person ages, changes hair, grows a beard, loses weight, or attempts cosmetic alteration.
That does not mean biometric systems are flawless, because privacy advocates, courts, and regulators continue debating accuracy, consent, retention, bias, transparency, and the risk of mission creep across airport and public surveillance systems.
Yet in high-security border environments, the technology can be powerful because it does not rely entirely on whether an officer remembers a fugitive’s old photograph or notices that a passport has been manipulated.
The scanner sees a structured comparison problem, not a nervous traveler, which is why a disguise that appears persuasive to a person may still produce a mismatch inside an automated inspection system.
The fugitive’s mistake was believing that a new face only needed to fool human memory, when modern border control increasingly asks whether the face matches the identity architecture behind the travel document.
European airports have become laboratories for biometric border control.
The new biometric border era has not arrived smoothly because travelers across Europe have reported longer lines, confusing kiosk procedures, repeated registration problems, and frustration as airports adjust to digital entry and exit processes.
A recent Reuters report on Europe’s biometric border rollout described how non-EU travelers must register personal details, fingerprints, and facial images under the new system, with subsequent travel relying more heavily on biometric verification.
For ordinary travelers, the immediate concern may be inconvenience, especially when families, elderly passengers, business travelers, and frequent flyers face longer processing times during the transition to automated systems.
For fugitives, document fraud networks, sanctioned individuals, and people traveling under unsupported identities, the concern is far deeper because the same delays and checks create more opportunities for mismatches to be noticed.
The airport queue may be frustrating for tourists, but for a traveler carrying a false identity, it can become the narrow corridor between old deception and immediate detention.
A surgically altered appearance is not the same as a new biometric identity.
Cosmetic surgery can change visible appearance, but it does not automatically erase the deeper continuity of a person’s facial structure, movement habits, scars, biometrics, fingerprints, voice patterns, gait, travel history, or documentary trail.
A person attempting to defeat border systems through surgery may change enough to confuse casual observers while still leaving a measurable relationship between the old identity and the person standing at inspection.
That risk becomes even greater when biometric systems are combined with passport chip validation, watchlist alerts, airline reservation data, previous visa files, entry records, fingerprints, and international law enforcement notices.
The practical lesson is that physical alteration creates more questions than certainty because an appearance that seems engineered can itself become suspicious if the travel story, document history, and biometric comparison do not align.
A changed face may open a door in a crowd, but it can close at passport control when the machine asks whether the body and the document belong to the same legal life.
The document may look perfect, but the database may disagree.
Modern border inspection is no longer limited to examining paper quality, holograms, watermarks, chip integrity, machine-readable zones, and photographs, although those document-security features remain important.
The more decisive question is whether the document exists cleanly inside the wider network of issuing records, watchlists, stolen document files, visa histories, prior crossings, and biometric enrollment data.
Interpol’s stolen and lost travel document systems, national passport databases, Schengen alerts, immigration records, and airline data can create friction even when a physical document appears convincing to the eye.
A counterfeit passport, stolen passport, fraudulently obtained genuine passport, or altered identity document may therefore fail not because the paper looks wrong, but because the story behind it cannot survive a database check.
The new border does not merely inspect the passport, because it interrogates the relationship between the passport, the person, and the records that should connect them.
The human officer still matters because machines do not make the whole arrest.
Biometric technology may create the alert, but trained officers still decide how to handle the traveler, preserve safety, review documents, ask questions, coordinate with supervisors, and determine whether the case requires detention, referral, or further investigation.
That human layer matters because false positives, data-quality issues, lighting problems, old photographs, name similarities, and system errors can affect legitimate travelers, making procedural safeguards essential.
A responsible border system must balance security with due process, because a mismatch should trigger careful review rather than automatic assumption that the traveler is criminal.
In the fugitive case, however, the mismatch was only the beginning because officers then examined supporting records, travel behavior, document provenance, and identity history until the false persona began unraveling.
The arrest was not made by a camera alone, because the camera opened the file that human investigators then built into a case.
The “ghost” was caught because the new identity had no real history.
A false identity can look strong when it is reduced to one document, but real life produces layers of history that are difficult to fabricate consistently across time.
Banks, border authorities, employers, landlords, insurers, tax agencies, telecom providers, hotels, and travel systems all expect an identity to have continuity, including prior addresses, financial behavior, lawful tax records, credible travel patterns, and consistent documentation.
When those layers are missing, thin, recycled, or inconsistent, the false identity begins to look less like a person and more like a construction built for one immediate purpose.
The airport mismatch exposed the deeper problem because the passport could not explain the person, the person could not explain the history, and the history could not explain the risk signals attached to the journey.
That is why serious identity fraud collapses under scrutiny, because a fake name can be printed quickly while a real life takes years of lawful records to build.
The case shows why fake passports have become bad investments for criminals.
Underground document sellers often market fake passports as premium products because they appear to promise travel, banking access, hotel registration, corporate formation, and personal reinvention.
The modern reality is harsher because every border, bank, platform, and regulator is becoming more capable of checking whether a document is supported by the deeper identity signals that should exist behind it.
The buyer may pay for paper, but what they need is a credible legal history, tax continuity, source-of-funds documentation, biometric consistency, clean travel records, and lawful identity connection across multiple systems.
A fake passport cannot provide those elements because it is only an image of legitimacy, not legitimacy itself.
The more advanced border control becomes, the more a forged passport turns from a travel tool into a high-risk artifact that can trigger detention, investigation, and prosecution.
Biometric borders are also reshaping lawful privacy planning.
The rise of facial recognition does not mean privacy is dead, because it means privacy must be planned through lawful identity, careful travel behavior, consistent documentation, and controlled disclosure rather than unsupported aliases or counterfeit documents.
For legitimate travelers facing stalking, extortion, kidnapping threats, hostile media, political targeting, or reputational danger, anonymous living strategies can reduce unnecessary exposure while preserving truthful disclosure where required.
This distinction is critical because lawful privacy protects people from unnecessary public visibility, while criminal concealment tries to hide fraud, warrants, false documents, or undisclosed identity history from authorities.
A traveler can be private and compliant at the same time, but a traveler using a fake passport is neither private nor secure once the document meets a serious inspection system.
The future belongs to people whose privacy plans can survive questions, not people whose identities depend on avoiding them.
The biometric age is forcing governments to balance security and civil liberties.
Facial recognition at borders is expanding because governments want faster processing, stronger identity checks, better detection of impostors, and more accurate records of who enters and exits their territory.
At the same time, regulators and privacy advocates continue raising concerns about data retention, consent, transparency, algorithmic accuracy, demographic bias, and whether biometric systems designed for borders might spread into ordinary public life.
The U.S. government’s own CBP biometric privacy guidance reflects how biometric border systems are now a normal part of travel-policy discussion, with official agencies explaining how facial comparison is used and how traveler data is handled.
The debate matters because a system powerful enough to catch impostors can also become controversial if the public does not trust how images are stored, shared, protected, or deleted.
The challenge for governments is to catch the ghost without turning every lawful traveler into a permanent suspect.
Criminals who once relied on appearance now face identity ecosystems.
The old fugitive playbook relied on changed appearance, cash, aliases, foreign residence, forged papers, quiet travel, and avoidance of predictable social patterns.
The new enforcement environment adds biometric comparison, airline data, automated risk scoring, document chip validation, lost passport checks, visa records, hotel reporting, financial intelligence, and international police cooperation.
That does not mean every fugitive will be caught instantly, but it means the margin for error is shrinking because one weak point can connect the false identity back to the person behind it.
A face mismatch can lead to a document review, a document review can lead to a database query, a database query can lead to an alert, and an alert can lead to investigators who already know what they are looking for.
The ghost is no longer fighting one officer at one booth, because they are facing an ecosystem designed to compare identity from every available angle.
The lesson for high-risk travelers is consistency, not concealment.
People with lawful reasons to protect privacy must understand that border systems reward consistency because names, documents, travel behavior, tax records, banking records, residence history, and device behavior all create a picture of credibility.
A traveler who uses lawful documentation, carries coherent records, controls unnecessary exposure, and answers questions truthfully is in a stronger position than someone relying on a story that cannot survive verification.
For individuals seeking a lawful reset, new legal identity planning can help align documentation, banking continuity, residence planning, and travel behavior into a structure that remains private without becoming deceptive.
The difference matters because a lawful identity can be verified discreetly, while a false identity must avoid verification entirely.
In the biometric era, avoiding verification is becoming harder with every new gate, camera, database, and border record.
The final lesson is that the unblinking eye sees patterns, not excuses.
The fugitive at passport control believed the false passport, altered face, and rehearsed story would be enough because older border systems often depended heavily on documents and human perception.
The biometric scanner changed the equation by asking whether the face, document, records, and travel history belonged to one coherent person.
That question exposed the weakness of the disguise because identity is not a costume, a passport page, a new haircut, or a surgical adjustment, but a living structure of records that must remain consistent across systems.
For criminals, the message is that fake documents are becoming more dangerous to use because every serious checkpoint can turn them into evidence.
For lawful travelers, the message is different and more useful, because privacy in 2026 is still possible, but only when it is built on legitimate documents, disciplined exposure, accurate records, and a life that can withstand the unblinking eye at the border.